Access Control Systems For Integrated Security Management
ICT access control systems redefine building security with an advanced all-in-one platform designed to protect people, assets, and infrastructure.
Trusted by organizations worldwide






What is Access Control?
Access control is a security process that keeps people, assets, stock and information safe. It employs robust authentication and authorization to ensure that only approved individuals can gain access to premises and resources. When done well, access control systems should minimize risk to your business and be scaled to your business' growth.
How Access Control Works
Building access control systems operate by identifying individuals or entities, verifying their identities, and authorizing access to areas based on predefined access rights. The process involves several key steps:

Identification
The first step involves identifying the individual attempting to access a resource through various means, such as user IDs, smart cards, or biometric data.

Authentication
Once identified, the system authenticates the identity of the individual by verifying their identification against the system records.

Authorization
After authentication, the access control system checks whether the individual has access rights to the area, granting or denying access based on the pre-defined rights.

Auditing
The final step involves logging all access attempts, both successful and unsuccessful. This provides a record of all access activity, which is essential for monitoring, compliance, and forensic analysis.
Why Choose ICT for Access Control?
Controlling who has access to your facility is a critical part of maintaining safety, security, and operational efficiency. ICT's advanced access control technology gives businesses full visibility and control over every entry point.
Whether you're a small business, a multi-site enterprise, or part of a complex industry, our scalable access control solutions integrate seamlessly with your unique security infrastructure to enhance overall system performance.
Benefits of a Protege system:
- Reduce the need for costly upgrades through seamless scalability
- Get added functionality with third-party integrations
- Gain extra cost savings by integrating with your Building Management Systems
- Sync data with external sources for a single source of truth
- Grant access or control the property remotely via web or phone
- Respond instantly to problems through mobile or monitoring service
Discover Our Access Control Platforms
ICT's Protege solutions are open-platform, scalable, and future-ready, providing a comprehensive solution for modern security challenges.
Enterprise Access Control
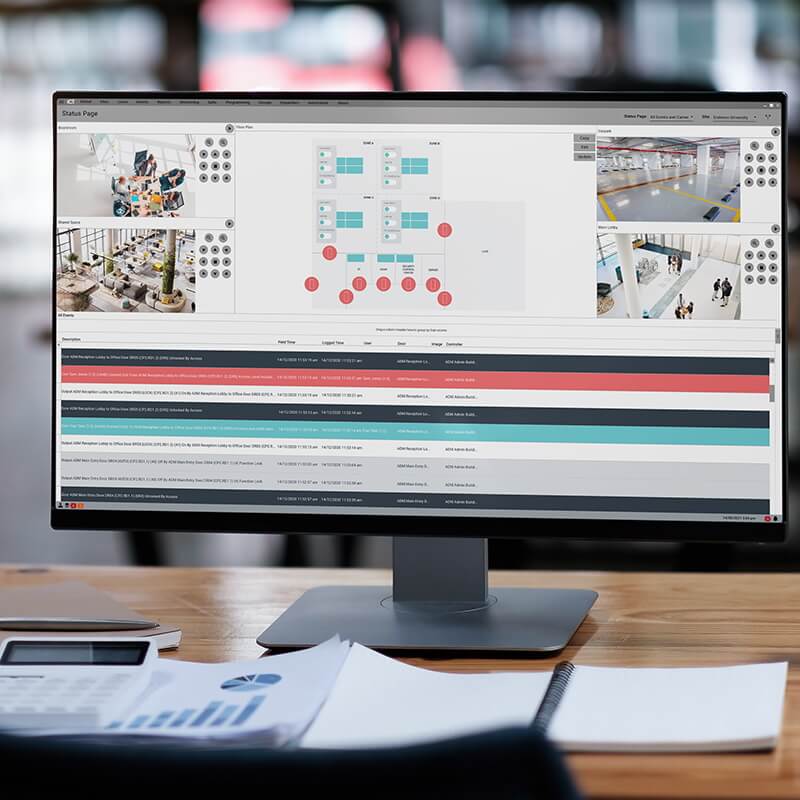
Protege GX
Easy to operate security system
Protege GX is a server based architecture, loaded with features that enhance the system further and enables you to securely manage, control and monitor a scalable number of users, doors and areas in real time.
Intuitive interface
Protege GX offers an intuitive and user friendly interface with graphical floor plans and highly customizable status pages for controlling and monitoring.
Extensive integrations
ICT's open architecture supports seamless integration with third-party solutions, such as video surveillance, maximizing the reach of your security technology.
Learn more about Protege GX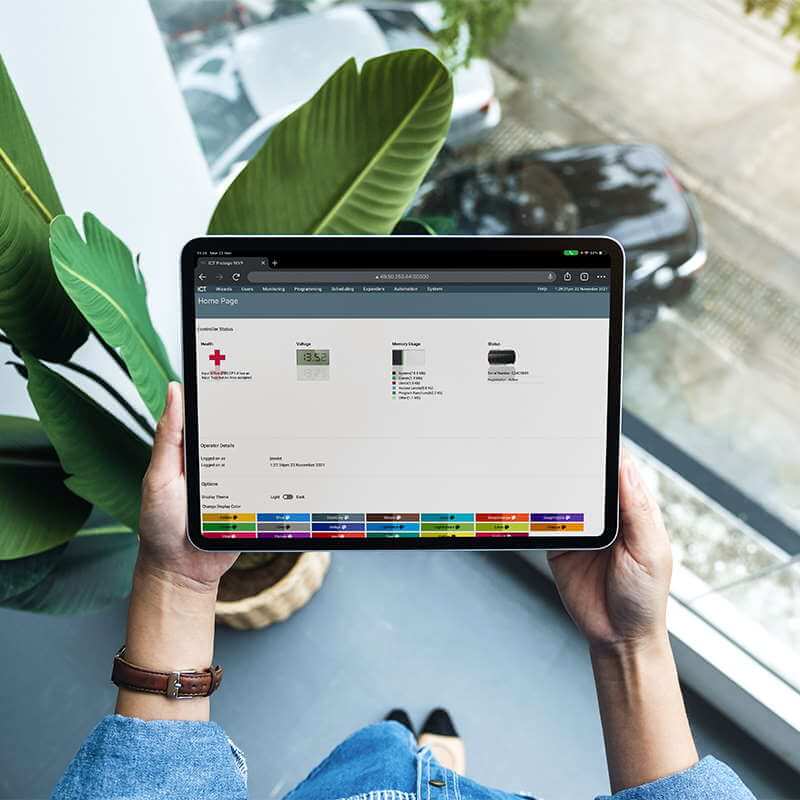
SMB Access Control
Protege WX
Simple to Install Security
Protege WX is a flexible, all-in-one, web based system that grows with you - effectively placing the office in the pocket of owners and operators.
Quick setup
Protege WX is an out-of-the-box system which means it's quick to set up, less than 5 minutes.
Learn more about Protege WXExplore Our Integrated Access & Security Solutions
ICT's open architecture integrates with the technology you already have — and everything you might add in the future.

Access Control Readers

Video Management Systems
- Unified Platform: Manage video surveillance and access control together for a streamlined, end-to-end security solution.
- Real-time visibility: Link video feeds with access events to instantly verify who accessed which area and when.
- Incident Response: Enable faster investigation by syncing access logs with recorded footage for accurate, time-stamped evidence.
Controllers, Expansion Boards, and Hubs

Wireless Sensors and Locking Solutions
- Simplified Installation: Reduce time and costs with wireless solutions that integrate seamlessly.
- Proactive Monitoring: Integrate wireless sensors to detect motion, door status, or environmental changes that trigger access control responses.
- Scalable Security: Easily expand your door and entry access control footprint across multiple sites or buildings with centralized management.
- Enhanced Security: Receive real-time alerts and automate lockdowns or alarms when unusual activity is detected.

Wireless Locks

Building Management
- Smarter Control: Integrate building management systems (BMS) with access control to automate lighting, HVAC, and energy usage based on occupancy.
- Centralized Oversight: Manage card access, security, and building operations from a single unified platform for streamlined facility management.
- Improved Efficiency: Trigger building responses like climate control or lighting—when users badge in or out, enhancing comfort and reducing costs.
Simplifying Access Control Management
ICT's Protege systems make managing multiple users and sites straightforward with intelligent software and mobile technology.
Remote Unlock Capabilities
Manage door locks remotely, initiate site-wide lockdowns, or modify access permissions from any web-based device, wherever you are.
Comprehensive Credential Support
ICT supports encrypted cards, fobs, and mobile credentials, ensuring secure, versatile access options that cater to different needs.
24/7 Access Monitoring
With real-time activity reports, alarm management, and mustering capabilities, ICT's platform provides total visibility and situational awareness across all access points.
Biometric Access Solutions
Link biometric credentials to access control to prevent unauthorized door access and eliminate the risk of lost or shared cards. Enable fast, touchless authentication for staff and visitors using facial recognition or fingerprint scans. Seamlessly integrate biometric data for centralized oversight and reporting.
Advanced Authentication
Biometric Access Solutions
Elevate security with biometric verification that makes credential sharing and unauthorized access virtually impossible. ICT integrates with leading biometric partners to deliver fingerprint, facial recognition, and multi-factor authentication.
- Stronger Security: Link biometric credentials to access control to prevent unauthorized door access and eliminate the risk of lost or shared cards.
- Frictionless Entry: Enable fast, touchless authentication for staff and visitors using facial recognition or fingerprint scans.
- Unified Management: Seamlessly integrate biometric data for centralized oversight and reporting.

Access Control Compliance & Security Standards
ICT solutions are thoroughly tested to meet the strictest international government regulations, ensuring you don't have to worry about certifications or compliance. Leave that to us — we've got you covered.
- UL294 for Access Control System (USA)
- ULC 60839-11-1 Alarm and Electronic Security Systems
- Fire Reporting ULC-S559 (CA)
- ULC-S304 Intruder Detection (CA)
- OSDP verified for tSec Reader
- IP65 Anti-ligature and Vandal Resistant
Frequently Asked Questions
What are the four types of access control credentials?
- Something You Know — Information only the user knows, such as a password, PIN, or security question answer.
- Something You Have — A physical item the user possesses, like a keycard, smartphone, RFID tag, or security token.
- Something You Are — Biometric data unique to the user, such as a fingerprint, facial recognition, iris scan, or voice recognition.
- Somewhere You Are — Access based on the user's location, determined through IP address, GPS, or network access point.
These credentials are often combined in multi-factor authentication systems for stronger security.
What maintenance is required for access control systems?
- Regular System Inspections — Check hardware components like card readers, locks, biometric scanners, and control panels for signs of wear or damage. Test doors and entry points to ensure proper locking/unlocking mechanisms.
- Software Updates — Apply firmware and software updates to fix bugs, enhance security, and improve functionality. Update the access control management software and any integrated systems (e.g., CCTV or alarms).
- User Access Review — Regularly audit user access rights to ensure only authorized individuals have access. Remove inactive users or update permissions when employees change roles or leave the organization.
- Battery and Power Backup Checks — Inspect and replace batteries in wireless components and backup power systems. Ensure uninterruptible power supplies (UPS) are functional in case of outages.
- System Testing — Conduct routine functional testing of readers, sensors, alarms, and door locks. Simulate unauthorized access attempts to verify alert and lockdown features work properly.
- Data Backup — Schedule regular backups of system configuration and access logs to prevent data loss. Store backups securely, preferably in an offsite or cloud location.
- Cleaning and Physical Care — Clean devices like keypads and biometric readers to maintain performance. Ensure access points are free from physical obstructions or vandalism.
- Documentation and Reporting — Keep logs of all maintenance activities, software updates, and hardware replacements. Use these records for compliance audits and system troubleshooting.
Routine maintenance extends the lifespan of your access control system and ensures it continues to protect your premises effectively.
Why is access control important?
Access control is important because it protects people, property, and sensitive information by restricting access to authorized users only. It enhances security, ensures safety, provides accountability through access logs, improves operational efficiency, and helps organizations comply with legal and industry regulations.
Talk to us about your access control requirements
Whether you're a system integrator looking for a solution to sell, a consultant looking for a secure platform to specify, or an end-user looking for an intuitive tool to keep your people and your property safe - a Protege solution can benefit your organization.
If you have any questions, would like further information, or would like to schedule a demo with one of our sales team, enter your details and we'll be in touch shortly.
Secure your future.

Free Resource
Access Control 101 — The Guide
Not sure where to start?
- What is access control and why it matters
- Evolution of access control and system components
- Credential types and security considerations
- Expanding your system through integrations
- Choosing the right solution for your organization
Next Steps

Have a question?
Access our knowledge base and get answers from our technical support team.

Want to see it in action?
Book a live demonstration and see what ICT solutions can do for you.

Ready to buy?
Request pricing tailored to your project requirements.

Want to get certified?
Become a certified Protege installer and grow your business.